Your traditional email security just became obsolete. While you've been fighting yesterday's phishing attempts with keyword filters and signature-based detection, cybercriminals have unleashed AI-powered attacks that make those old-school scams look like amateur hour.
Here's the stark reality: 43% of cyberattacks now target small and medium businesses, and AI-generated phishing emails are slipping past standard defenses at an alarming rate. These aren't your typical "Nigerian prince" emails anymore. Modern AI can craft personalized, contextually relevant messages that even security-conscious employees struggle to identify.
But here's the good news: you don't need weeks of training or a massive security overhaul to protect your business. With the right approach, you can significantly strengthen your defenses in just five minutes.
Why AI-Powered Phishing Attacks Are Different
Traditional phishing relied on mass-produced emails with obvious red flags: poor grammar, generic greetings, and suspicious links. Your spam filter could catch most of these because they followed predictable patterns.
AI has changed everything. Modern phishing tools can:
- Generate perfect grammar and natural language that reads like legitimate business communication
- Research your company and employees using publicly available information to create highly targeted messages
- Mimic writing styles of trusted contacts, vendors, or industry partners
- Create realistic-looking websites and landing pages in minutes
- Adapt in real-time based on your responses and behavior patterns
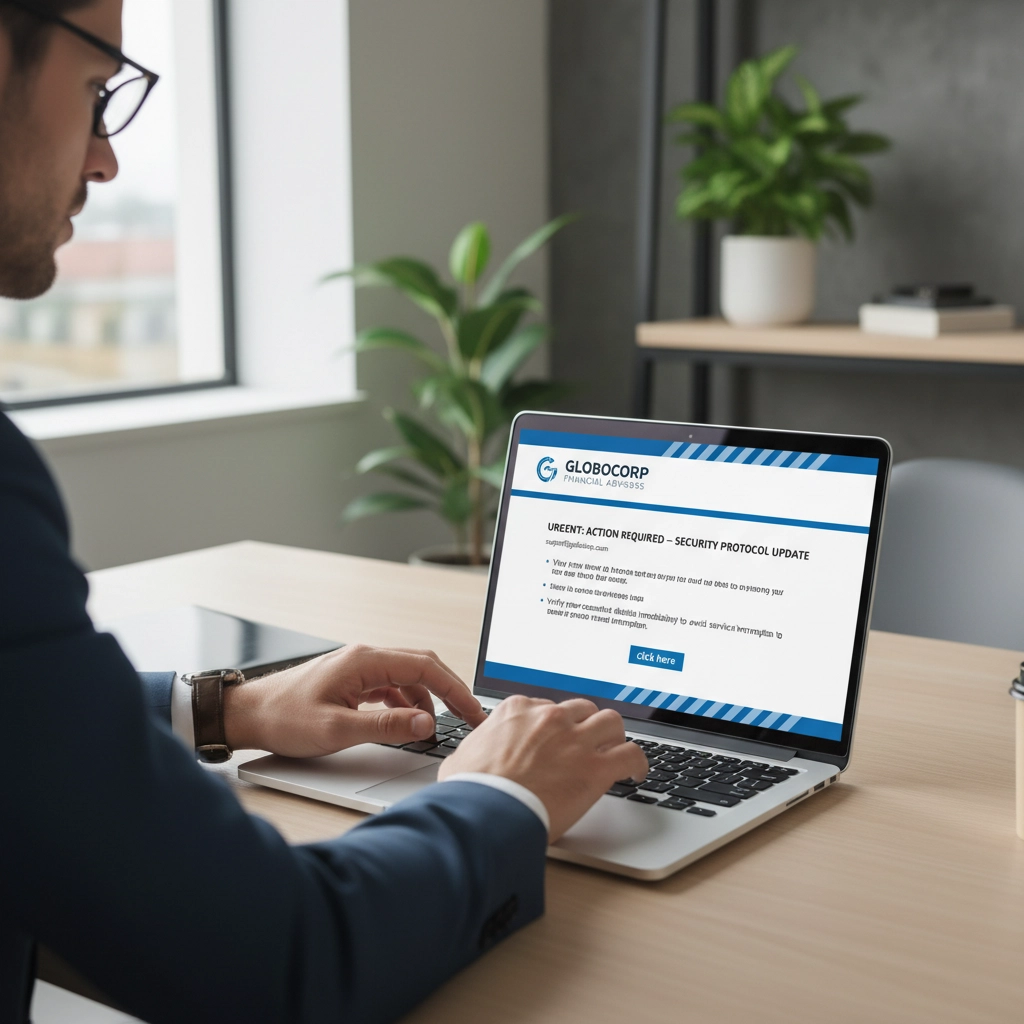
The result? Phishing emails that are virtually indistinguishable from legitimate communication. Your employees receive messages that appear to come from familiar contacts, reference recent company events, and request actions that seem perfectly reasonable in context.
These sophisticated attacks bypass traditional email filters because they don't contain typical spam indicators. Instead, they use social engineering psychology combined with AI's ability to craft convincing narratives tailored specifically to your business environment.
Your 5-Minute Defense Strategy
Step 1: Implement AI-Powered Email Security (2 minutes)
Replace your basic email security with an AI-enhanced solution that uses behavioral analysis and machine learning. Unlike traditional filters that rely on known threat signatures, these systems ask: "What action is this email trying to get someone to take?"
Look for solutions that offer:
- Real-time link analysis that scans URLs when clicked, not just when received
- Attachment sandboxing that opens suspicious files in isolated environments
- Email authentication through SPF, DKIM, and DMARC protocols
This upgrade immediately blocks AI-generated threats that slip past keyword-based filters. Many cloud-based solutions can be deployed in minutes through your current email provider's security settings.
Step 2: Enable Phishing-Resistant Multi-Factor Authentication (1 minute)
Move beyond SMS-based two-factor authentication immediately. CISA now recommends FIDO/WebAuthn or passkeys because they're virtually impossible for AI-powered attacks to bypass.
Here's why this matters: Even if attackers successfully steal your employees' passwords through sophisticated phishing, they still can't access your systems without the cryptographic keys stored on physical devices or biometric authentication.
Set this up through your current business applications: most major platforms now offer one-click FIDO setup that takes less than a minute per user.
Step 3: Configure Email Authentication Standards (1 minute)
Set up SPF, DKIM, and DMARC records to prevent attackers from impersonating your domain. This stops criminals from sending emails that appear to come from your business address.
Your IT provider or email host can configure these DNS records quickly. This single step prevents brand impersonation attacks that could damage your reputation and trick your customers or partners.

Step 4: Brief Your Team on AI-Powered Threats (1 minute)
Conduct a quick team briefing about new AI-powered attack methods. Focus on these key points:
- Verify unexpected requests through known channels: never confirm sensitive actions through the original email
- Watch for subtle urgency tactics: AI excels at creating plausible time pressure
- Question perfect personalization: if an email knows too much about your recent activities, verify independently
- Be suspicious of QR codes: these bypass many email security scans
Emphasize that these attacks will look and sound legitimate. The goal isn't to spot obvious scams but to verify anything that requests sensitive actions or information.
Advanced Protection Strategies for Long-Term Security
Implement Zero-Trust Email Verification
Adopt a "verify everything" approach to email communications. This means treating every email as potentially suspicious until verified through independent channels, regardless of the sender's apparent identity.
Create verification protocols for common business actions:
- Financial requests require phone confirmation using known numbers
- Credential resets must be initiated through official portals, never email links
- Vendor communications need verification through established contact methods
Deploy Continuous Security Monitoring
AI-powered attacks evolve rapidly, so your defenses must adapt continuously. Implement monitoring systems that track unusual email patterns, unexpected login attempts, and behavioral anomalies across your organization.
Modern security platforms use machine learning to establish baselines for normal business communication patterns. When something deviates: like an executive suddenly requesting wire transfers or an employee accessing unusual systems: the system flags these activities for immediate review.

Establish Incident Response Procedures
Create clear procedures for when employees suspect phishing attempts. This includes:
- Immediate reporting channels that don't rely on email
- Isolation procedures for potentially compromised accounts
- Communication protocols for notifying customers and partners if needed
Quick response times significantly reduce the impact of successful attacks. Every minute counts when dealing with AI-powered threats that can spread through your network rapidly.
Why This Approach Works Against AI-Powered Attacks
Traditional security focused on identifying known threats. AI-powered email security flips this approach by analyzing behavior and intent rather than looking for specific signatures or keywords.
This creates a dynamic defense system that adapts to new attack methods automatically. When AI generates a new type of phishing email, your security system learns from the attempt and updates its detection algorithms across your entire organization's email environment.
Real-time enforcement adds another crucial layer. Even if a sophisticated email reaches someone's inbox, protective measures activate when they click suspicious links. The browser displays warnings and blocks access to malicious sites, preventing credential theft even when users fall for convincing attacks.
The Bottom Line: Speed Matters in Cybersecurity
AI-powered phishing attacks exploit the gap between when new threats emerge and when traditional security systems update their databases. By implementing behavioral analysis and real-time protection, you eliminate this vulnerability window.
Your five-minute investment in upgraded security measures creates a foundation that adapts automatically to emerging threats. This proactive approach protects your business without requiring constant manual updates or extensive training programs.
The cybersecurity landscape continues evolving rapidly, but these fundamental protection strategies remain effective because they address the psychology and methodology behind attacks rather than specific technical signatures.

Ready to strengthen your cybersecurity posture beyond these quick fixes? Explore our comprehensive cybersecurity training courses designed specifically for small and medium businesses. Our NIST Cybersecurity Small Business Essentials course provides detailed guidance on implementing enterprise-level security practices that scale with your business growth.
Don't wait for an attack to expose your vulnerabilities. These five minutes of action today could save your business from months of recovery tomorrow.